About me

As a lawyer with experience building and securing applications and automations, I'm uniquely qualified to bridge the gap between legal compliance and technical implementation. I build custom software and workflows that solve bottlenecks while keeping you compliant with local and international regulations. From data security to digital infrastructure, I guide you through the complexities so you can focus on what matters.
What have I built? A variety of things, from enterprise custom software to internal tools and e-commerce platforms. Markatzy, an AI-powered platform using RAG architecture to automate trademark monitoring and legal defence. Websites for businesses of all sizes, tailored to their needs with privacy and security at the core. At Kriptos, I supported SOC 2 Type II certification by monitoring security controls and triaging vulnerabilities, then transitioned to the dev team where I delivered 37,000+ lines of production code for the Update Manager module.
My toolkit? Legal expertise, experience working at the edge of what's possible with today's tech, a cybersecurity postgraduate diploma from UT Austin, software engineering and cybersecurity diplomas from BrainStation (Konrad Group), a financial accounting certificate from HBS Online, a cloud certification from AWS, ongoing training for CompTIA Security+, and an obsession with efficiency.
Outside of work, I'm an explorer and the outdoorsy type. Long-distance running, volcano hikes, and easy days at the beach with my wife.
View Resume Blog Let's ConnectProjects
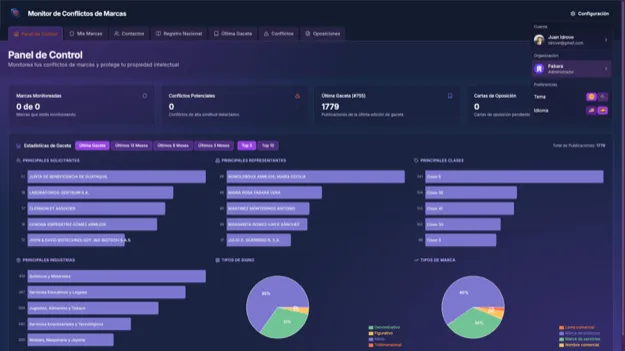
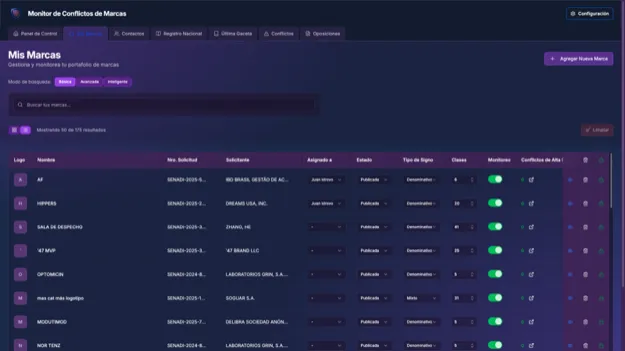
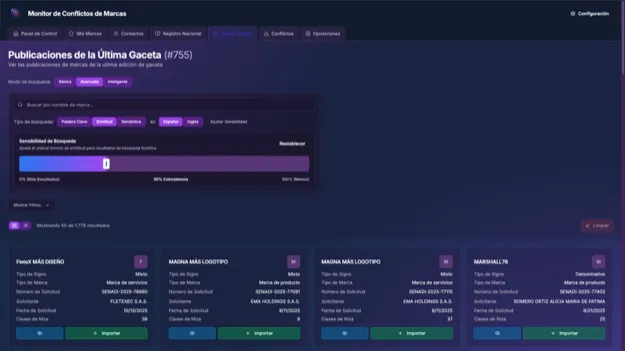
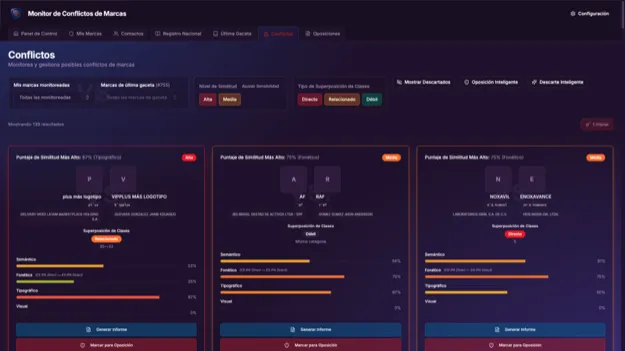
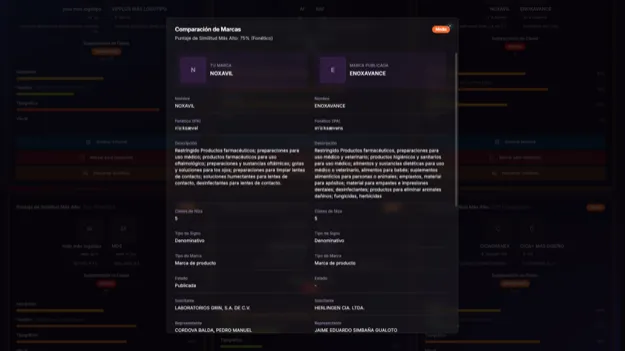
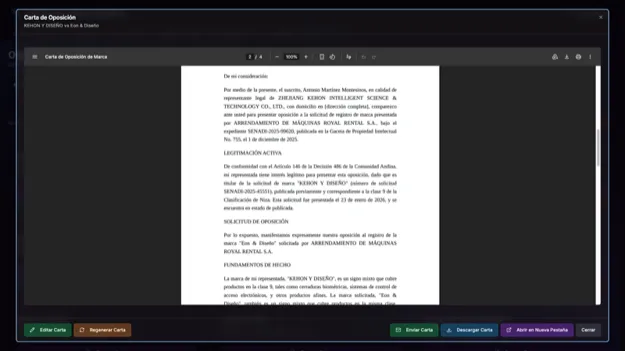
Markatzy Legal AI SaaS
AI-powered trademark protection platform with real-time, multi-dimensional conflict detection. Analyzes brands across phonetic (IPA-based, cross-language), typographic, semantic (vector embeddings), and visual dimensions. Searches over half a million trademarks in under 100ms with enterprise-grade security (rate limiting, row-level data isolation). A-rated in SonarQube for maintainability, reliability, and security. Built with RAG architecture (Retrieval-Augmented Generation), Next.js 15, type-safe APIs (tRPC), vector databases (pgvector), and OpenAI for intelligent conflict analysis.
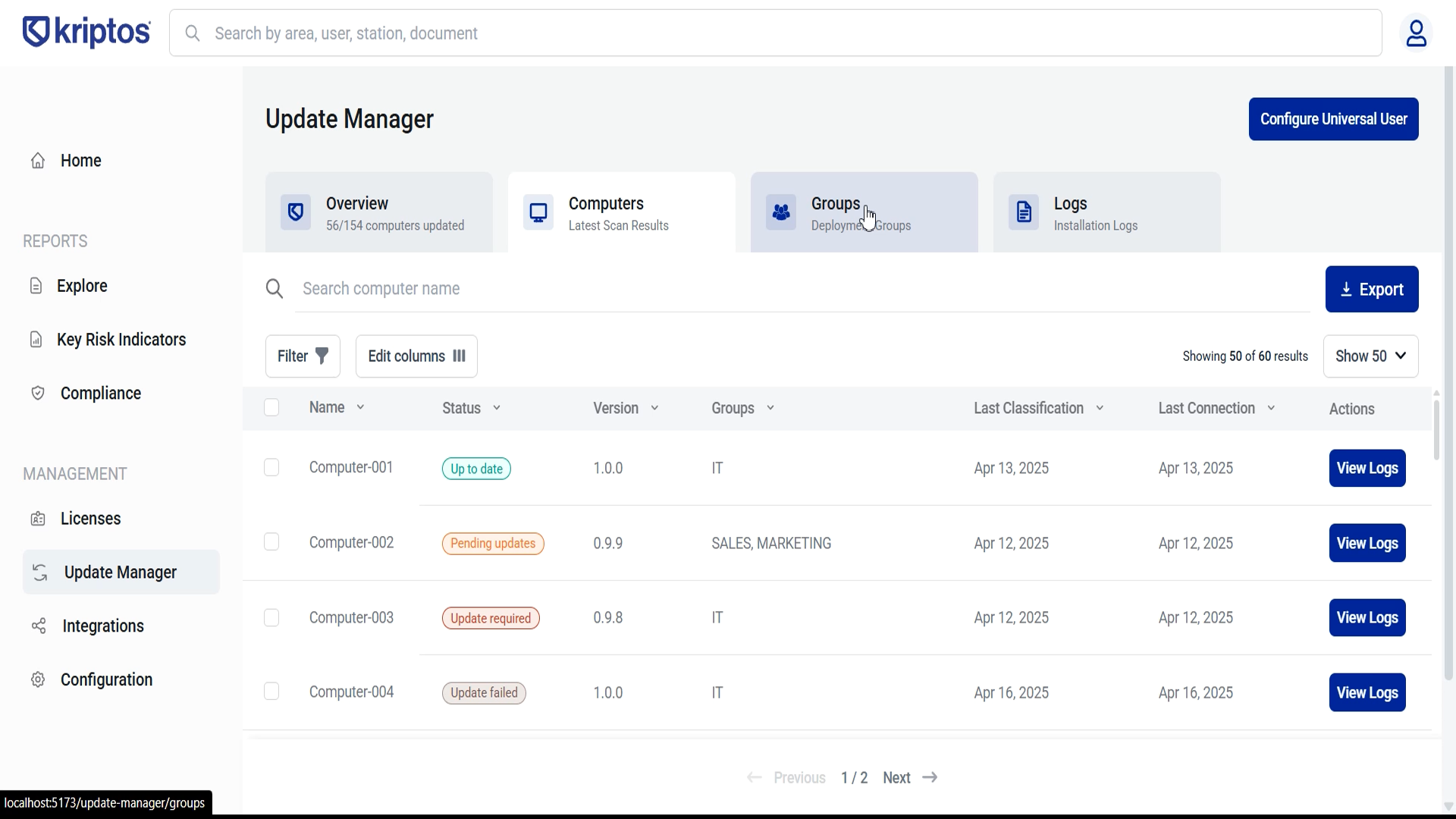
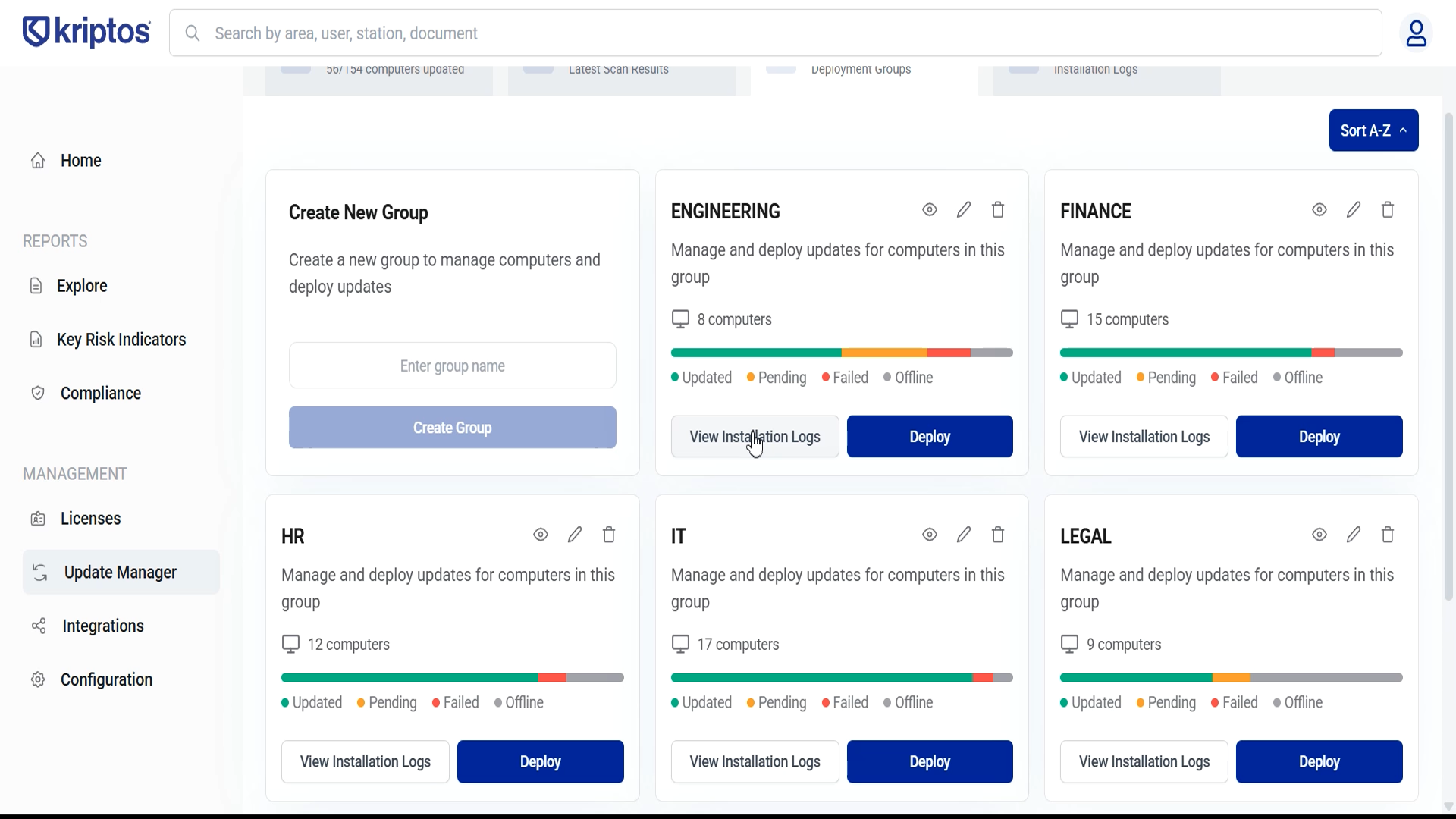
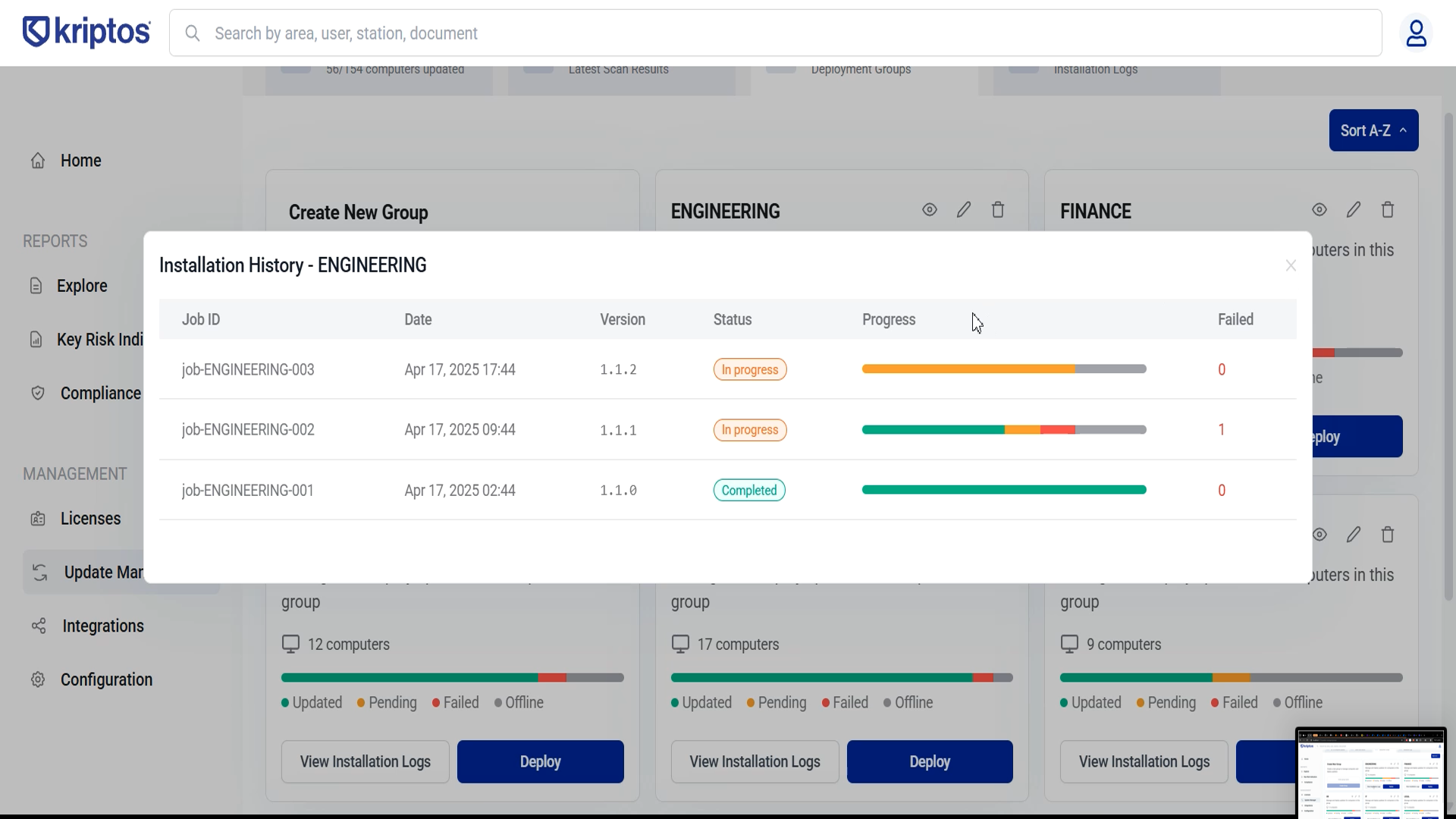
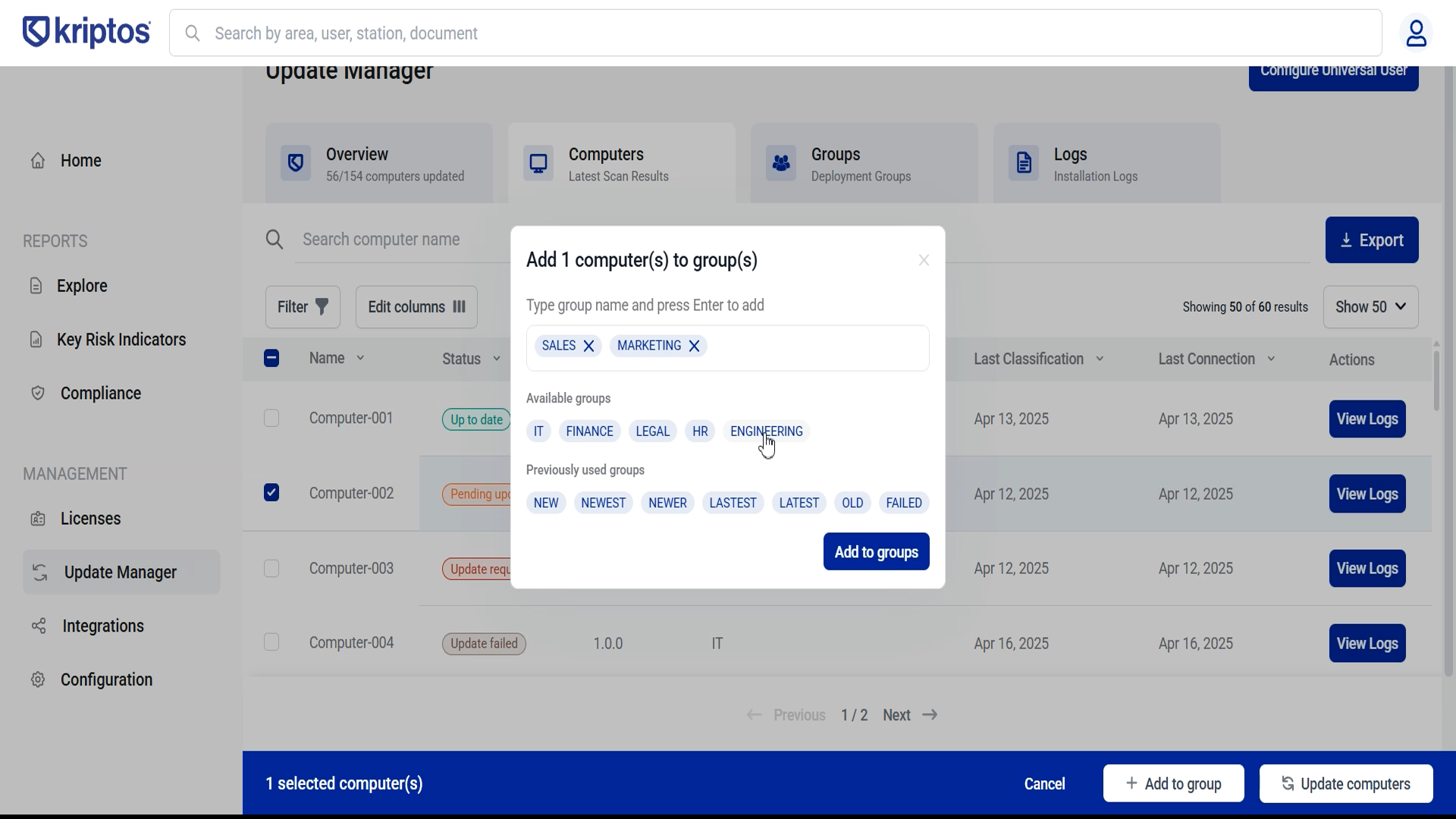
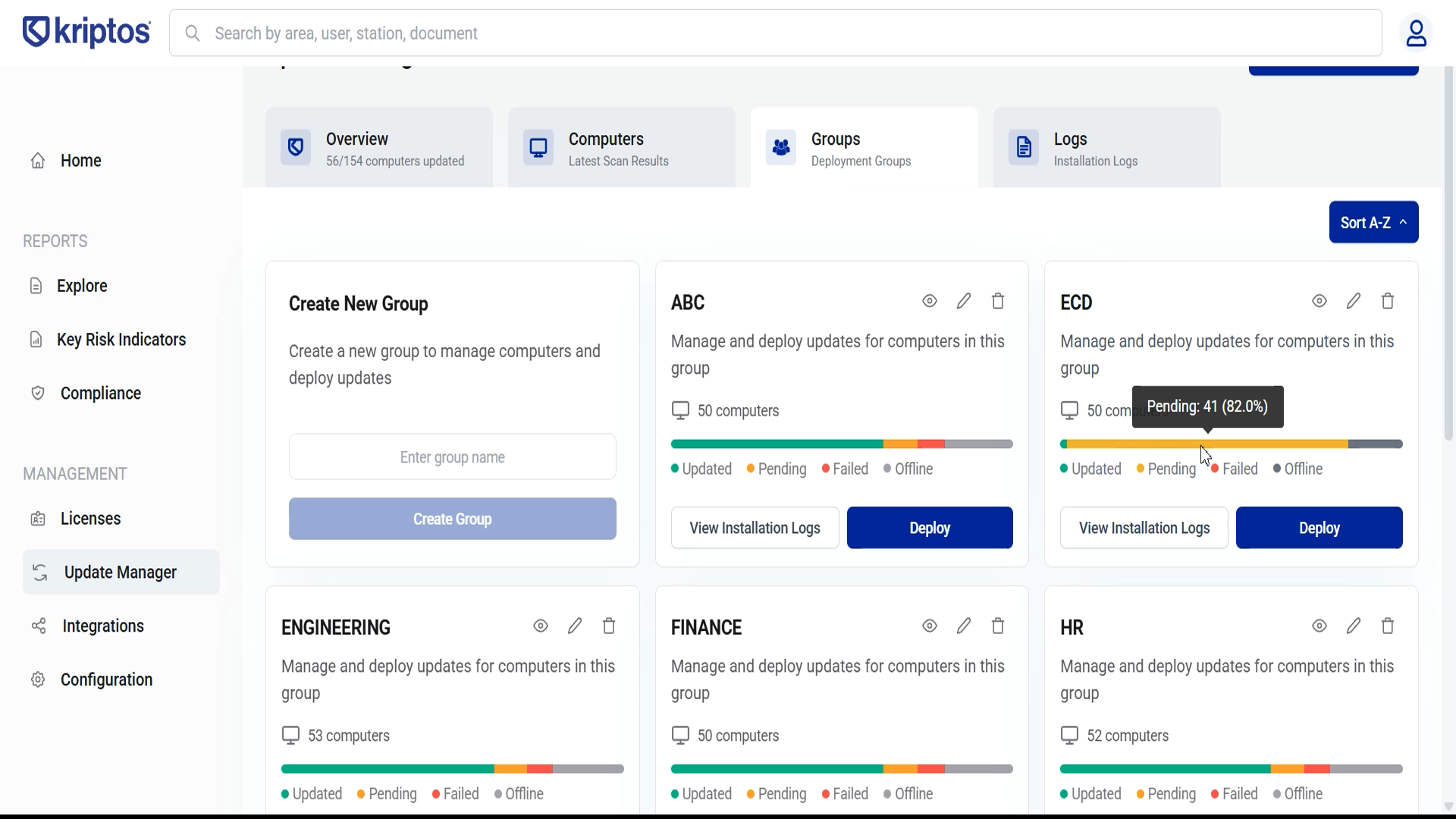
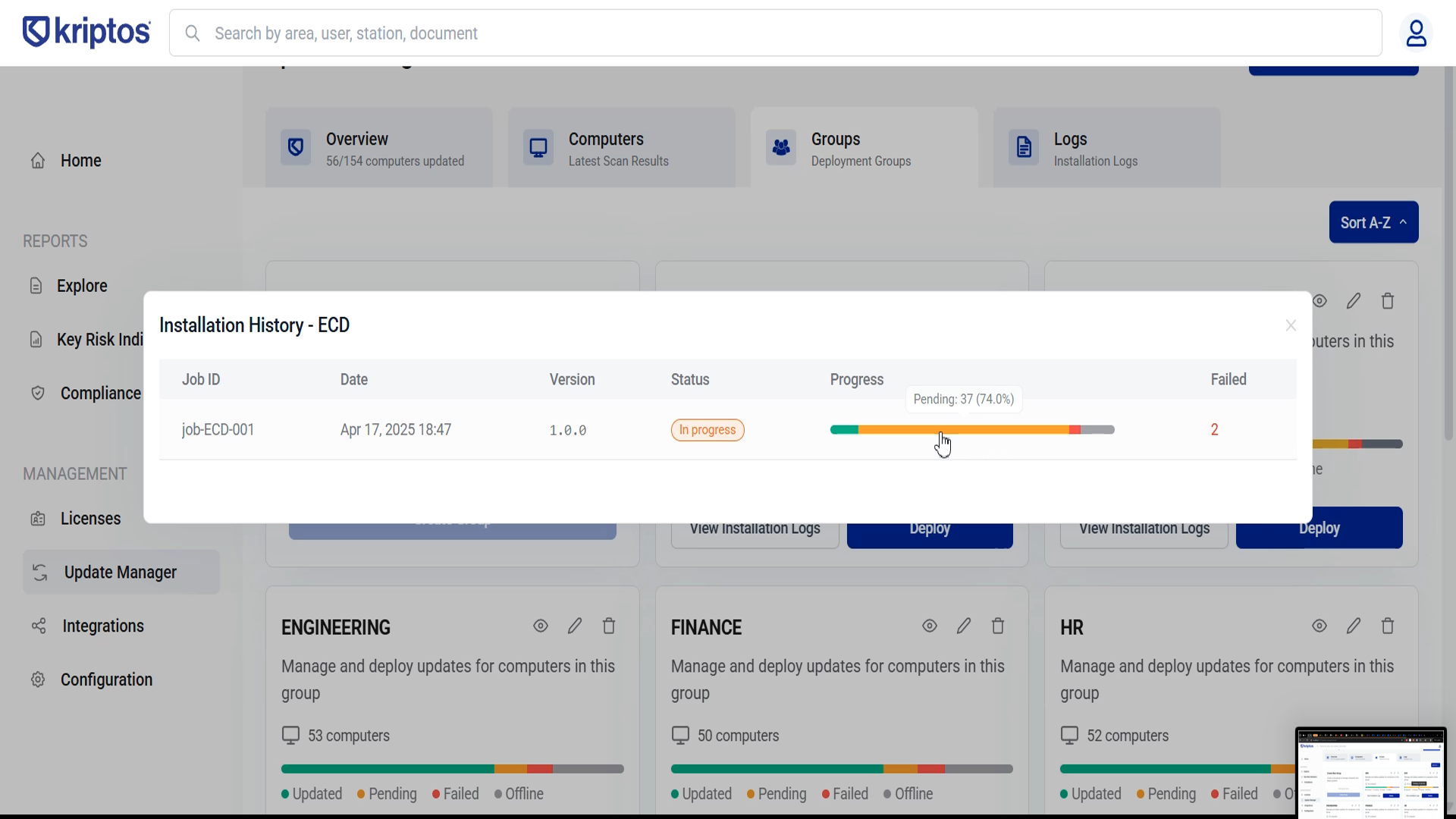
Update Manager Enterprise Tool
Windows agent installation orchestrator built for Kriptos Inc. Enables IT departments to securely deploy and manage software across thousands of client computers at banks and multinationals. Led frontend development with 219 commits and 37,000+ lines of code.
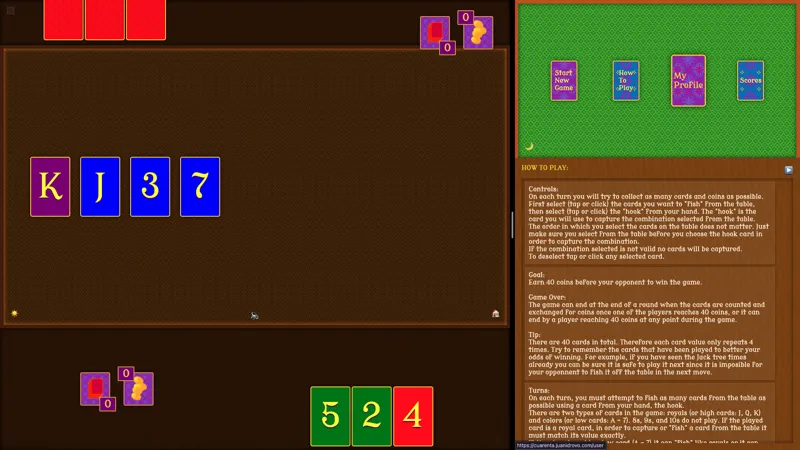
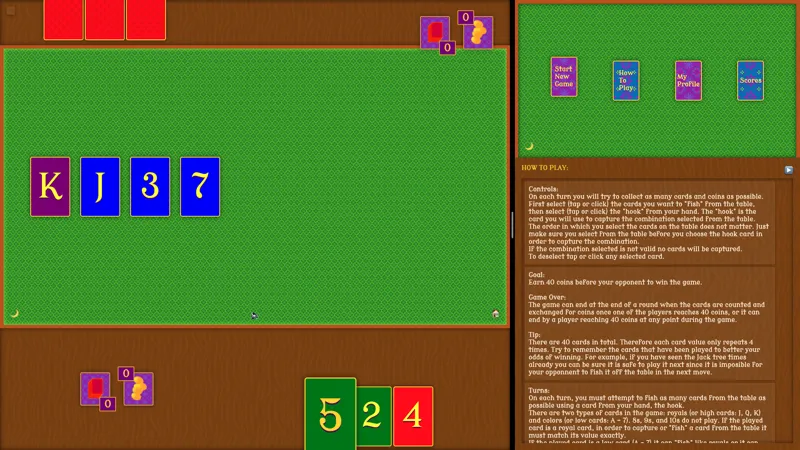
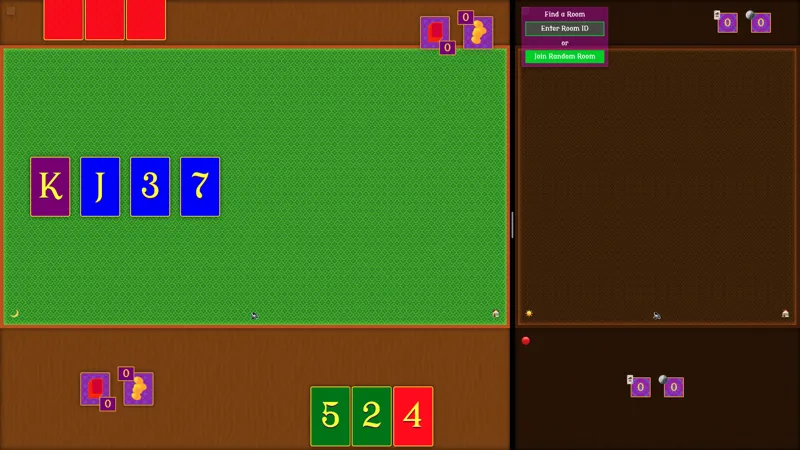
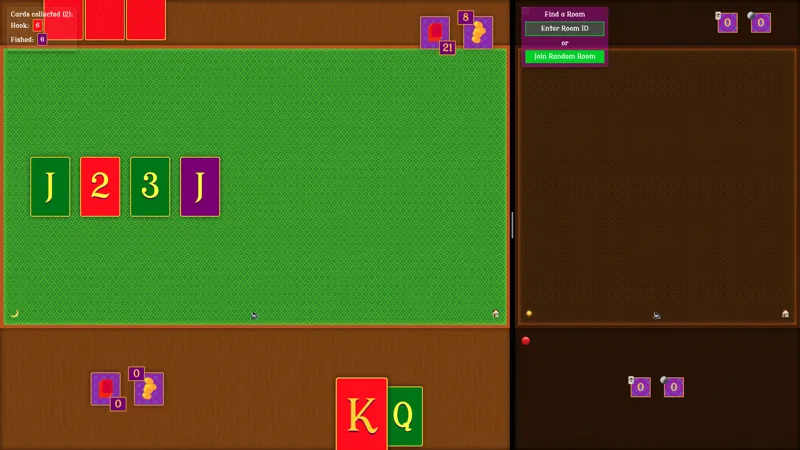
Cuarenta Card Game
Digital implementation of the traditional Ecuadorian card game, built in 2 weeks during BrainStation bootcamp. Features real-time multiplayer with WebSockets and AI opponents. React, Node.js, Express.
Grace Nelson Law Website
Complete website and digital infrastructure for a bilingual expat-focused law firm with 22+ years of experience. Features multi-language support (EN/ES), appointment booking integration, WhatsApp messaging, secure contact forms, property listings, and video testimonials. Also built internal workflow automations and CRM systems.
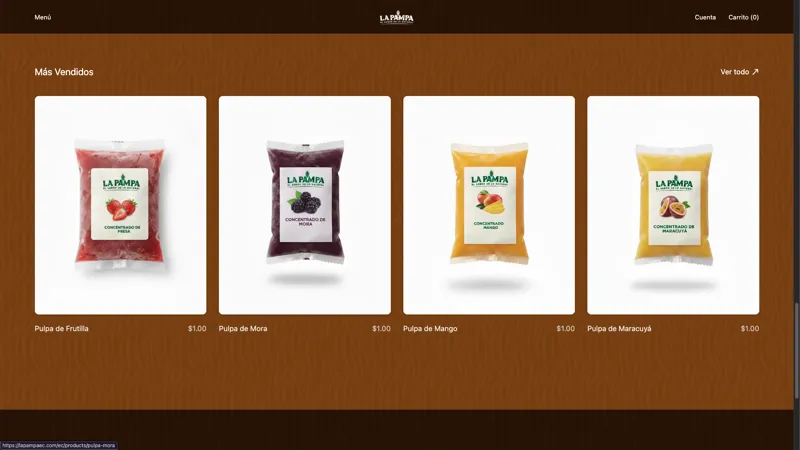
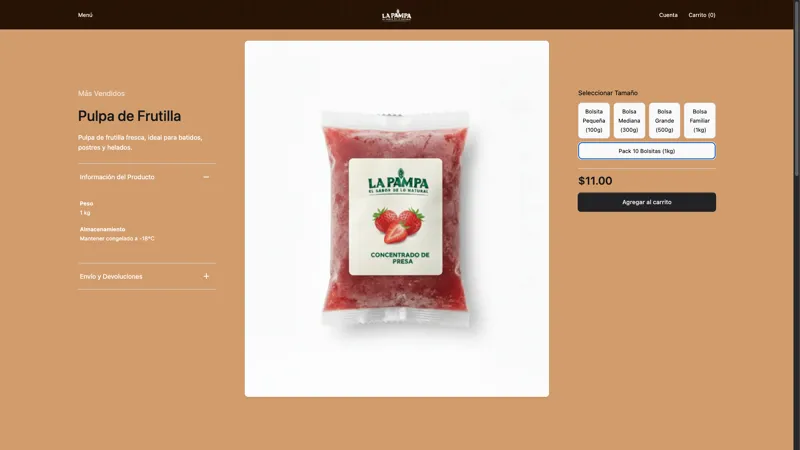
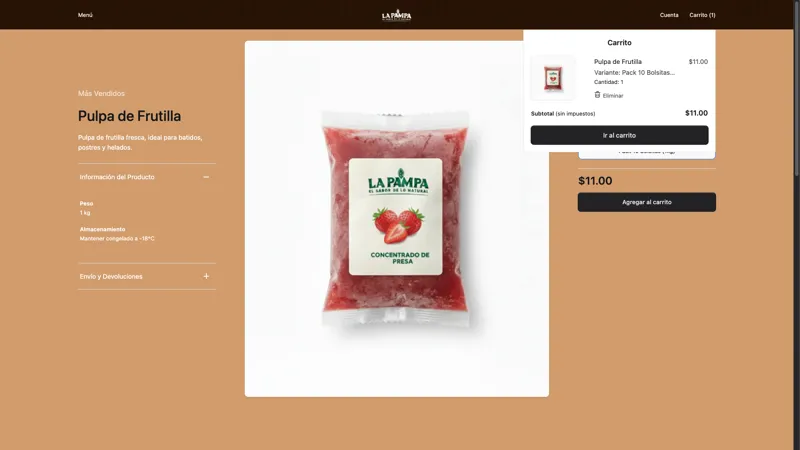
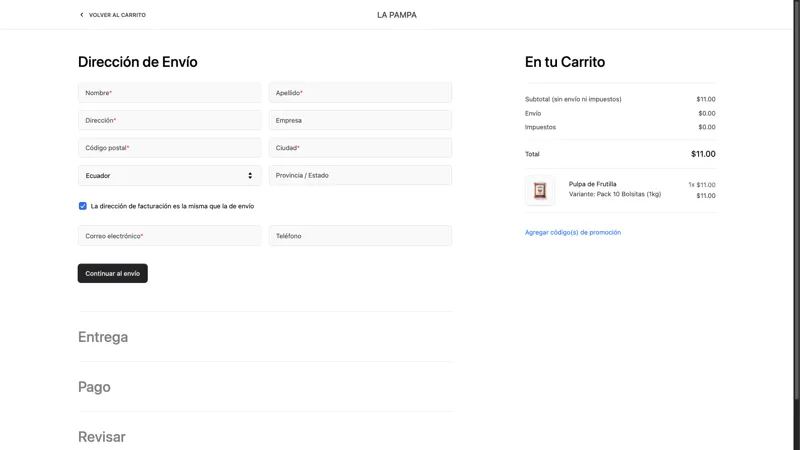
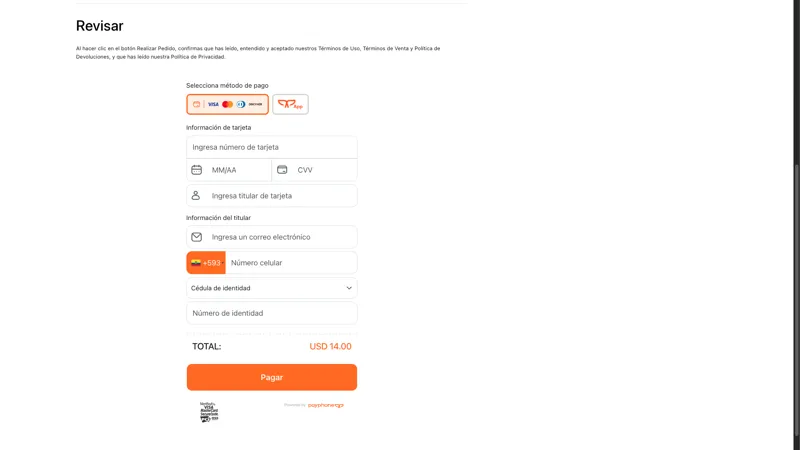
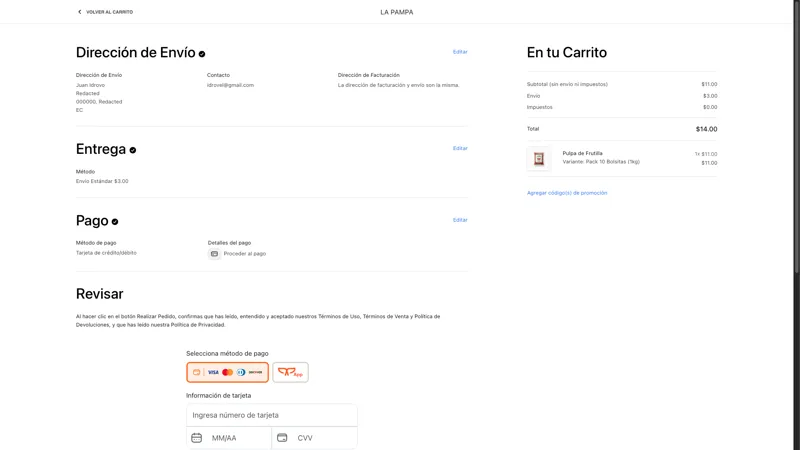
La Pampa E-commerce
Full-stack e-commerce platform for a frozen fruit pulp producer. Next.js 15 storefront with Medusa.js v2 headless backend. Features product catalog, cart, checkout, PayPhone payments, and admin dashboard. Deployed on Railway with PostgreSQL and Redis.
Frequently Asked Questions
Do I need SOC 2 or ISO 27001?
It depends on your target market. SOC 2 is what US enterprise buyers expect in procurement. If you're selling SaaS or handling data for US clients, start there. ISO 27001 carries more weight in Europe and internationally. Many companies pursuing both start with SOC 2 for quicker wins, then layer on ISO 27001 for global reach. Read more
How long does SOC 2 certification take?
A realistic timeline is 3–6 months for Type I and 6–12 months for Type II, depending on your current security posture. Type I covers policy design and a point-in-time audit. Type II adds an observation period (3–12 months) where controls must operate effectively. Companies in emerging markets often need extra time to formalize policies and choose tooling. Read more
What is the difference between SOC 2 Type I and Type II?
Type I evaluates whether your security controls are properly designed at a specific point in time. Type II evaluates whether those controls operated effectively over a period, typically 3 to 12 months. Enterprise buyers generally require Type II because it demonstrates sustained operational security, not just a one-time snapshot. Read more
How much does SOC 2 certification cost?
Costs typically range from $20,000 to $100,000+ depending on company size, scope, and readiness. Major cost drivers include compliance automation tooling ($10,000–$30,000/year), auditor fees ($10,000–$50,000), and internal effort for gap remediation. Startups with clean cloud-native infrastructure tend toward the lower end. Read more
Do I still need SOC 2 if I use AWS or Azure?
Yes. Cloud providers operate under a shared responsibility model. AWS and Azure secure the infrastructure, but you're responsible for data handling, access controls, application security, and operational procedures. A SOC 2 audit evaluates your controls, not your cloud provider's.
Is SOC 2 required by law?
No. SOC 2 is a voluntary framework developed by the AICPA. It's not mandated by any law or regulation. That said, it's become a de facto requirement in B2B software sales. Enterprise buyers, investors, and procurement teams routinely require a SOC 2 report before signing contracts.
Can a startup get SOC 2 without a dedicated security team?
Absolutely. Many startups achieve SOC 2 using compliance automation platforms like Vanta, Drata, or Secureframe that handle evidence collection, policy templates, and continuous monitoring. A single engineer or operations lead can typically manage the process with some external guidance.
Does ISO 27001 make you GDPR compliant?
They overlap in areas like access control and incident management, but ISO 27001 alone doesn't cover GDPR's specific requirements: data subject rights, legal bases for processing, cross-border transfers, and supervisory authority reporting are all outside its scope. Read more
How does the EU AI Act affect companies outside Europe?
The EU AI Act applies to any company whose AI systems are placed on the EU market or whose outputs are used within the EU, regardless of where the company is headquartered. This extraterritorial reach follows the GDPR model, meaning companies outside Europe selling AI-powered products to EU customers must comply. Read more
What legal risks should AI products prepare for?
AI products face legal exposure across intellectual property, data privacy, and regulation. Key risks include copyright claims over training data, liability for AI-generated outputs, GDPR violations, and emerging AI-specific laws like the EU AI Act. Establishing clear data provenance and compliance frameworks early is critical. Read more
Contact
Let's build something secure, and ship it.
Let's Talk